Protection & detection with SOCaaS
Stay ahead of threats with InterVision’s expert SOC Team. 24/7 monitoring stops attacks before they happen. Our dedicated, experienced team utilizes industry-leading tools for precise detection and containment.
Ransomware recovery as a service
Your business is always protected: Managed resiliency 24/7. Our expanded approach includes air gapping, MFA, and immutable backups for enhanced recovery.
Strategic support with a vCISO
With InterVision, a skilled CISO leads your RPaaS Business Risk Reduction program, guiding your team through security analysis, advice, and roadmap planning. They are ready to assist in executing a response strategy during a ransomware event, ensuring your business stays protected.
Disaster recovery landing zone
Should your primary datacenter become inaccessible for forensic evidence purposes, RPaaS includes a cloud-based Disaster Recovery Landing Zone to act as a secondary recovery datacenter in a scalable cloud solution.
A real-time customer attack recovered in 67-minutes
This real-time attack and recovery timeline below from one of our customers exemplifies how RPaaS broke recovery barriers and provided true RTO exceeding expectations.
-
-
-
-
-
-
NOTE
NOTE
OPTIONAL capture of forensic data for analysis prior to recovery operations, dictated by legal counsel
-
-
6:30AM
6:30AM
Infected data recovered from immutable repository at recovery point before incident – scanned and confirmed clean
-
Fortify
Fortify
Security posture reviewed with client and a recommendation is made to geofence firewalls and block PowerShell via GPO
-
Outcomes
Detect and Protect:
Attack identified within 5 minutes. Full report with remediation recommendations to customer within 25 minutes.
Respond and Recover:
Compromise contained and 40TB file server restored in under 10 minutes after receiving customer go ahead.
Advise and Adapt:
Customer environment hardened against future attacks based on post-mortem findings.
Watch our Explainer video and learn more about RPaaS.
Why choose InterVision’s RPaaS?
InterVision’s Ransomware Protection as a Service (RPaaS) is the industry’s first and only holistic approach to ransomware threats, focused on the entire lifecycle of detection, protection, and recovery
- Most comprehensive approach available
- Backed by industry leading SLAs
- Trusted leader in data recovery

InterVision Cybersecurity Solutions
As cyber threats continue to grow in number and sophistication, it’s important to have the right level of protection in place. We offer three levels of cybersecurity solutions. Use our chart to compare features and find the right fit for your business.
Foundation | Professional | Enterprise | |
Builds a solid foundation for detection, and response to Cyber Threats. | Improves upon IV cybersecurity foundation by validating your cybersecurity plan and providing 24x7x365 professional remediation of vulnerabilities. | Adds to the IV cybersecurity professional offering with comprehensive and ongoing security posture management and recovery services to end downtime risk. | |
Managed Detection and Response (MDR) A security solution providing comprehensive threat monitoring, incident response, and expert analysis aimed at safeguarding businesses against cyber threats, serving as an alternative to an in-house Security Operations Center (SOC). | |||
Incident Response (IR) Retainer A proactive solution offering aimed at aiding in incident response plan preparation and providing priority cost-transparent incident response engagements without the need to pre-purchase hours, ensuring a 1-hour SLA response from expert engineers. | |||
Enhanced Cyber Threat Concierge Service A named resource is assigned to the account for the MDR solution to seamlessly integrate the InterVision Operations Center, Customer Success, Client Service, Professional Service, and other teams by providing regular ticket reviews, escalation, and relationship management. | |||
Penetration Testing Proactive vulnerability identification and root cause analysis through one-time or live testing and expert analysis. Continuous testing ensures ongoing risk management and business continuity while safeguarding customer and partner interests and improving ROI from security investments. | (1-time) | (Continuous) | |
Managed Device (Monitoring, Patching, Remediation) InterVision’s suite of Managed Network and Server solutions, combined with our MDR solution, provide end-to-end 24/7 expert detection, response, remediation, best practice review, and change management for client devices. | |||
Managed Helpdesk Provides personalized and effortless support, offering 24/7 access to expert personnel, industry-leading response times, and a single point of contact for all users, serving as a cost-effective alternative to in-house support. | |||
Endpoint Detection and Response (EDR) Streamlines risk mitigation, expediting threat containment, integrating malware protection, and enhancing ROI for businesses by leveraging expert detection, isolation of compromises, and proactive security measures. | |||
Monthly vCISO InterVision’s Cyber Consulting team engages with the client regularly to assist in the maturation of the client’s security profile, address business risks, and develop roadmaps for improvement. | |||
Disaster Recovery as a Service (DRaaS) Offers immediate disaster reaction, robust infrastructure protection, ongoing testing for compliance, and a customized recovery playbook, all backed by industry-leading SLAs to ensure recovery assurance. | |||
Fortify your business with InterVision’s Ransomware Protection as a Service (RPaaS)
Experience unmatched ransomware defense with InterVision’s RPaaS. Our all-encompassing service integrates advanced technology, round-the-clock rapid response, and customized strategies based on the NIST Cybersecurity Framework 2.0. Supported by top-tier SLAs and insurance coverage, we ensure swift recovery and minimal downtime, transforming potential weeks-long impacts into hours.
Download now to streamline your operations, evade ransom payments, and secure your business’s resilience against evolving cyber threats.

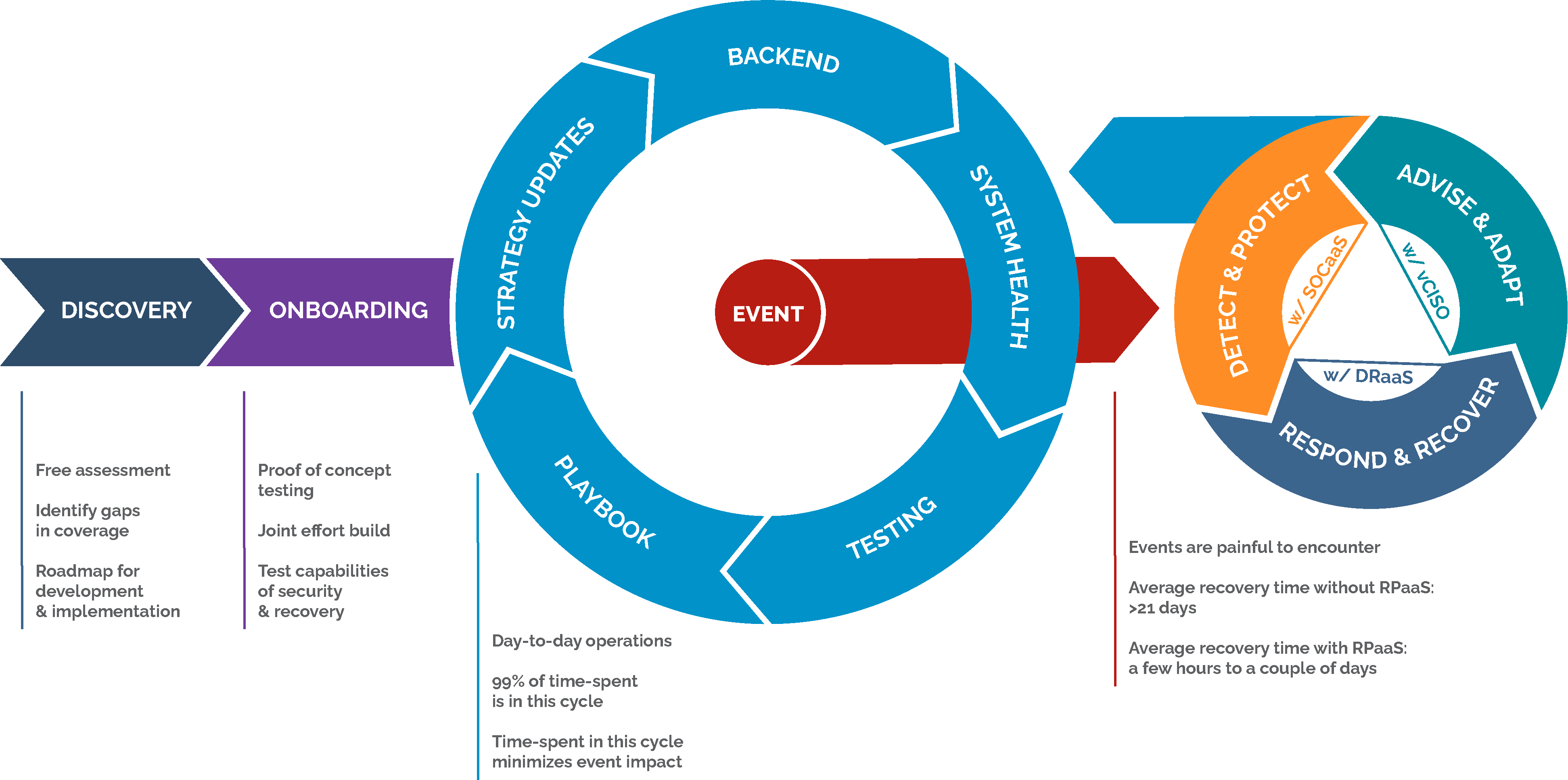
The RPaaS process
The RPaaS process is a proven comprehensive approach that is backed by industry-leading SLAs that support your business requirements.

Who we serve
InterVision delivers technology solutions and managed services to organizations across various industries, helping them enhance customer experiences today while driving innovation for the future. Some industries we help:
- Education: K-12, Higher Education
- Financial: Commercial Banks, CPA Firms, Credit Unions, Insurance Companies, Investment Firms, Private Equity Firms, Wealth Management Services
- Government: Local, State, Federal
- Healthcare: Hospitals, Medical Devices and Equipment, Nursing and Care, etc.
- Manufacturing: Consumer Goods and Services, Chemicals, Containers and Packaging, Industrial Machinery, etc.
Knowledge is power
Strengthen your defense against ransomware with proactive insights and solutions. Ransomware Protection as a Service helps you stay informed and resilient against evolving cyber threats, empowering your organization to recover quickly.
Your strategic partner for an AI-Driven future
InterVision combines technical excellence with a strategic, future-ready approach—empowering your organization to lead with confidence, agility, and results.
InterVision delivers leading AI services for every step of the journey, from getting started with AI to developing policies, leveraging hyperautomation via agentic workflows, and setting up POC environments- all aligned to your business goals.
Our team has decades of experience and hundreds of certifications with AWS, Microsoft, Cisco, Fortinet, Juniper, Arctic Wolf, HPE, and many more. No matter your challenge, InterVision can tailor innovative services using best-in-class technology solutions.
Remove obstacles to innovation and leverage InterVision expertise to take advantage of flexible financing choices, exclusive purchasing plans, and simplified marketplace transaction options.
Managed Innovation is InterVision’s unique approach to managed and professional services that drives IT excellence not just today, but into tomorrow. Our success is your success, and our expert team works diligently to continually evolve IT solutions that keep your company ahead of change.
Seamlessly navigate unforeseen IT change with pre-validated solutions from the InterVision NextMove program. Leave unwieldy vendor lock-in and unfavorable contracts behind, while pivoting to next-generations solutions that deliver better performance, costs, and outcomes.
InterVision is a trusted partner for state and local governments, K-12 schools, and higher education institutions. Our expert team can deliver pre-validated solutions and services that deliver better outcomes for constituents and meet complex regulatory challenges.